An Indispensable Tool for Successful Cybercrime Investigations
Cyber Threat Intelligence (CTI) provides a methodological bridge between technical analysis and criminal investigation. Much like digital forensics, CTI supports cybercrime investigations by placing technical traces into a structured context, thereby consolidating and prioritizing investigative leads.
The term Cyber Threat Intelligence (CTI) has long been established in the field of cybersecurity and has evolved into a discipline in its own right. Its roots lie in classical intelligence analysis methods combined with technical IT security research. CTI involves the structured process of collecting, processing, and analyzing information about adversaries to understand their motives, objectives, capabilities, and methods. CTI can therefore be described as a body of evidence-based knowledge1, aimed at providing context, indicators, mechanisms, and actionable recommendations for the protection of IT systems – enabling proactive response against known threat actors and future potential attacks.
Given the highly dynamic threat landscape in cyberspace, it is essential to apply CTI proactively, as perpetrators and threat groups continuously and rapidly adapt their methods to changing circumstances. For domains ranging from cybercrime and Crime as a Service (CaaS) to Advanced Persistent Threats (APTs), Cyber Threat Intelligence provides valuable insights into tactics, techniques, and procedures (TTPs).
In practice, CTI is often procured as an “Intelligence Product” from external cybersecurity firms. These providers supply comprehensive analyses of threat actors, their infrastructure, campaigns, and indicators of compromise. This data enables organizations to continuously adapt their defensive measures and maintain up-to-date risk assessments.
There is, of course, also the option of building proprietary CTI capabilities using a variety of open sources and free platforms such as MISP2 or OpenCTI3. However, this requires ongoing maintenance, dedicated personnel, and specialized expertise. Regardless of the technical approach, the central question remains: What significance does Cyber Threat Intelligence hold for law enforcement investigations?
Cybercrime Investigation and CTI
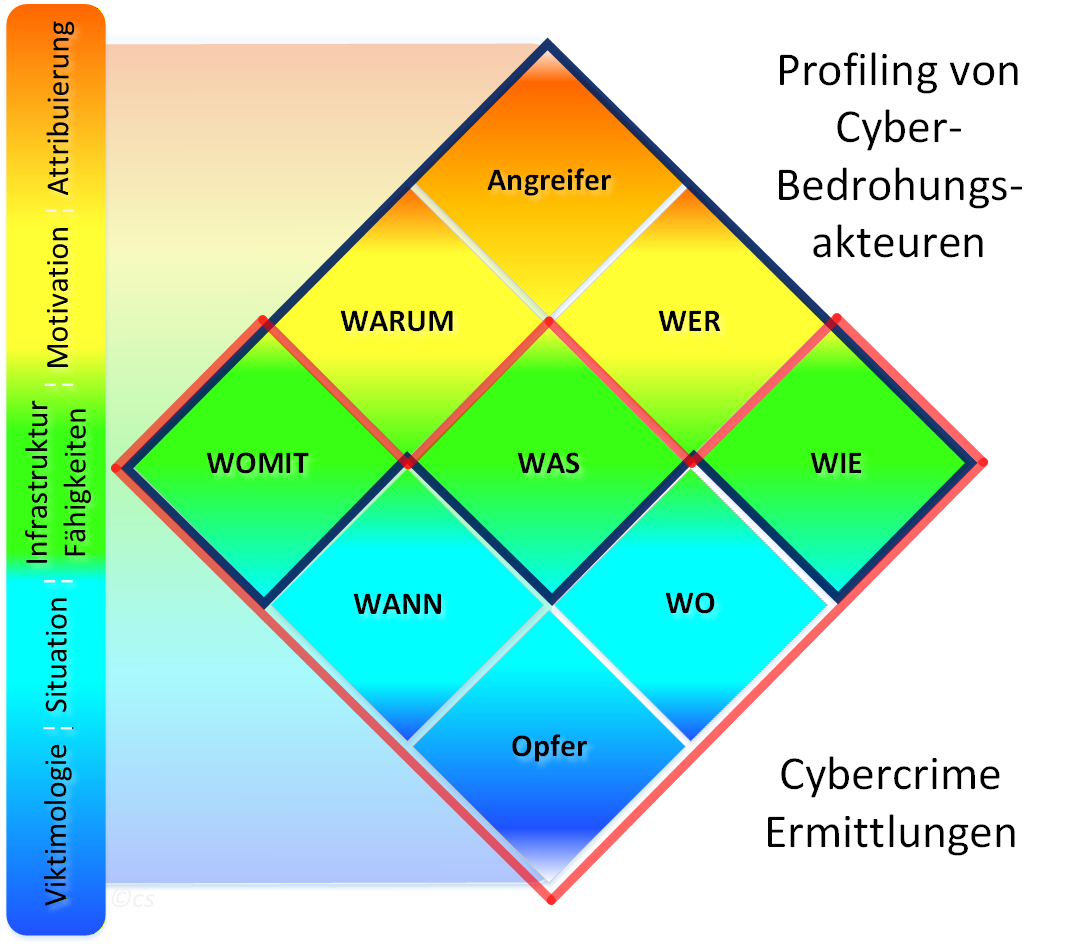
Within Cyber Threat Intelligence, the Diamond Model of Intrusion Analysis4 has become an established framework for describing and systematically analyzing cyber threats. This model characterizes incidents based on four core elements: adversary, capability, infrastructure, and victim. It can also be extended to include additional attributes such as time, phase, result, direction, methodology, and resources. This model complements the fundamentals of criminal investigation seamlessly:
Core concepts of traditional policing, such as the investigative framework of “Who, What, When, Where, How, With What, and Why,” are also applied in digital investigations. While analog evidence naturally remains relevant in criminal case work, the volume of potential digital evidence has increased exponentially over the past decades.
In cybercrime investigations, investigators typically begin with victimology, as they most often first determine – through a complaint or report – who or what was the target of the attack. The overall situation is then assessed to understand when and where exactly the incident occurred. Investigators attempt to reconstruct what exactly happened, how it was carried out, and what tools and techniques the perpetrators employed. This analysis serves not only to reconstruct the offense but also to assess the capabilities and professionalism of the actors involved. Furthermore, the indicators of compromise (IoCs) collected during the investigation can reveal leads – for example, identifying the technical infrastructure used to conduct the attack. Once the essential data points have been gathered, the motivation of the perpetrators can often already be inferred.
Digital investigations in the cybercrime domain are characterized by large volumes of data, high complexity, and the need for cross-border cooperation in both law enforcement and judicial contexts. Despite these challenges, the overarching goal remains attribution – the identification of a specific threat actor or group, or at least parts thereof.
CTI as an Integral Component of Modern Cybercrime Prosecution
When traditional cybercrime investigations are combined with Cyber Threat Intelligence methods, a unified analytical framework emerges. This framework integrates victimology, situational awareness, infrastructure and capability analysis, motive assessment, and attribution, enabling not only precise analysis but also proactive investigative approaches (where legally permissible).
Law enforcement agencies that systematically integrate CTI methods into their investigations gain deeper contextual insights, achieve breakthroughs more quickly, and strengthen their cooperation with academia and industry.
While every cybercrime investigator today should understand and be able to apply fundamental CTI principles, Cyber Threat Intelligence encompasses a wide range of specialized and primarily technical capabilities – such as Infrastructure Hunting (identifying the technical infrastructure used by perpetrators), Threat Actor Profiling (building adversary profiles), malware analysis, and OSINT research. These competencies can – similar to digital forensics – be efficiently concentrated in specialized units and deployed in a supporting capacity during investigations.
A comparable model already exists in the field of cryptocurrency investigations, which have established themselves as a distinct specialization in Austria and many other countries due to their complexity and rapid evolution. While fundamental concepts remain valid in the long term, the tools, patterns, and strategies of threat actors are constantly changing. Against this backdrop, it seems only logical to establish Cyber Threat Intelligence as a specialized discipline to support criminal investigations with a cybercrime nexus. CTI can provide targeted support to investigators in both the narrow and broader sense of cybercrime, making it a fundamental building block of modern, effective law enforcement in the digital space.
Conclusion
Cyber Threat Intelligence is not merely a technical tool of IT security but rather a logical evolution of traditional investigative work in the digital domain. In the face of increasingly professional, compartmentalized, and internationally operating criminal structures in cybercrime, a purely reactive approach to investigations is no longer sufficient.
Law enforcement agencies should therefore systematically integrate Cyber Threat Intelligence into cybercrime investigations. CTI makes it possible to link individual cases to broader campaigns, connect technical traces with threat actor profiles, and strategically prioritize both investigative leads and entire case complexes. This leads not only to faster attributions but also to sustained strategic intelligence gains regarding criminal structures and their methods of operation.
For effective digital policing in the cybercrime domain, the following points are essential:
- Establish CTI as a dedicated function supporting cybercrime investigations, comparable to digital forensics or cryptocurrency investigations.
- Leverage platforms such as MISP and OpenCTI for analysis and information sharing to maintain current situational awareness.
- Consolidate specialized CTI competencies to operationally support investigators (e.g., Threat Actor Profiling, Infrastructure Hunting, Malware Analysis).
- Expand cooperation with academia, CERTs, and industry through CTI channels to enable the exchange of strategic intelligence in a common language.
Anyone who seeks to effectively combat cybercrime must systematically understand threat actors, methods, and networks. Cyber Threat Intelligence provides the methodological framework for this – and is thus an indispensable component of modern law enforcement.
External Sources
Gartner defines Threat Intelligence as “evidence-based knowledge, including context, mechanisms, indicators, implications and actionable advice …” (cited from CrowdStrike, “Cyber Threat Intelligence Explained”): crowdstrike.com ↩︎
MISP (Malware Information Sharing Platform) for law enforcement agencies: misp-lea.org ↩︎
OpenCTI, an open platform for collecting, structuring, and analyzing CTI knowledge: github.com/OpenCTI-Platform ↩︎
Publication of the “Diamond Model of Intrusion Analysis” in 2013 by Sergio Caltagirone, Andrew Pendergast, and Christopher Betz: apps.dtic.mil ↩︎
